บริการฝากนำเข้าจีน-ไทย บริการฝากสั่งซื้อ
เรทราคา
พรีออเดอร์
(ให้บริษัทสั่งซื้อให้ นำเข้าให้)

ประเภทสินค้า
ทั่วไป
มอก
พิเศษ
ราคากิโล
20
30
60
ราคาคิว
7,000
7,500
10,000
ราคากิโล
15
20
-
ราคาคิว
5,000
6,800
-
เรทนำเข้า

ประเภทสินค้า
ทั่วไป
มอก
พิเศษ
ราคากิโล
15
25
60
ราคาคิว
6,500
7,000
9,000
ราคากิโล
10
15
-
ราคาคิว
4,000
6,000
-
VIP
VIP 1,999 บาท

ประเภทสินค้า
ทั่วไป
มอก
พิเศษ
ราคากิโล
10
20
40
ราคาคิว
6,000
6,500
9,000
ราคากิโล
8
15
-
ราคาคิว
4,000
5,500
-
คำนวณค่าขนส่ง
คำนวณค่านำเข้า
ราคากิโลขนส่งของลูกค้า
ราคาคิวขนส่งของลูกค้า
น้ำหนัก
กว้าง
ยาว
สูง

ทางรถ
ทางเรือ
เกี่ยวกับเรา
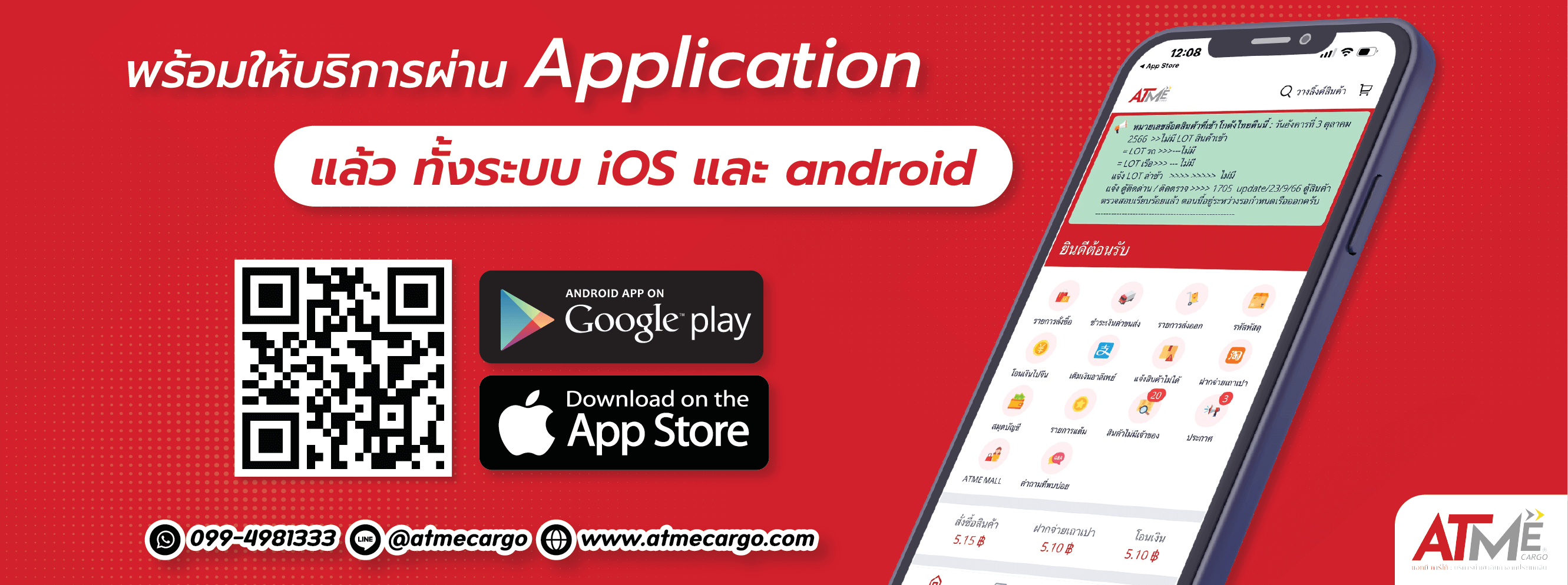
ATME CARGO:สั่งซื้อสินค้าจากจีน และบริการนำเข้าสินค้าจากจีน มาไทย
จากเว็บไซต์สั่งของชั้นนำจากจีน ผ่านระบบออนไลน์ที่ทันสมัย
เราอำนวยความสะดวกในการติดต่อและสั่งซื้อสินค้าจากร้านค้าหรือโรงงานในประเทศจีน
จากนั้นจัดการนำเข้าและจัดการเรื่องภาษีนำเข้าส่งถึงมือลูกค้าถึงที่อยู่ปลายทางในประเทศไทย
ไม่มีขั้นต่ำ ไม่มีปิดรอบ คิดน้ำหนักตามจริง ถูกตั้งแต่กิโลแรก มีระบบแจ้งเตือนสถานะ
นอกจากนี้เรายังให้บริการโอนและจ่ายเงินในสกุลเงินหยวนผ่านธนาคารทุกธนาคารในประเทศจีนไซต์สั่งของชั้นนำจากจีน
ไม่มีค่าโอนเงินระหว่างประเทศ รวดเร็ว ปลอดภัย 100%
ดูวิธีสั่งซื้อ